eDiscovery Trends: John Simek

This is the third of our Holiday Thought Leader Interview series. I interviewed several thought leaders to get their perspectives on various eDiscovery topics.
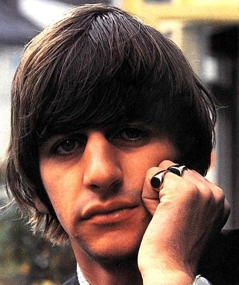
Today’s thought leader is John Simek. John is the Vice President of Sensei Enterprises, a computer forensics firm in Fairfax, Va, where he has worked since 1997. He is an EnCase Certified Examiner and is a nationally known testifying expert in computer forensic issues. Together with his wife, Sharon Nelson, John has become a frequent speaker on eDiscovery topics and digital forensic issues. We have also interviewed Sharon, who serves as Sensei’s President, for this series, and her interview will appear this coming Wednesday.
You have been a forensic examiner for a long time. How has the business changed over that time? How much does the rate of change in computer technology make your job difficult? Has social media and mobile technology changed the nature of your work and the evidence in play?
Certainly the technology changes present a challenge for any forensic examiner. We are constantly investing in training and tools to deal with the changing landscape. Social media investigations and mobile devices are explosive forms of evidence for many of our cases. The constant changes in smartphones means we must have dozens of tools to extract data from iPads, Androids, BlackBerrys, iPhones, tablets and other mobile devices. Access to social media data varies as well. Some is readily available in the public areas, some may reside on the actual computer used to access the social media sites and some data may be held by the providers themselves, where the user has no clue it is being collected.
There have been several cases of law firms and EDD providers suing each other of late. Why is there this seeming rise in conflict and how does it affect relationships in the industry?
I’ve only seen two such cases and they get ugly really quick. I think the primary reason is lack of transparency and adequate communication. The client should always know what the anticipated costs and effort will be. Should scope change then a new estimate needs to be communicated. I think all too often the EDD providers launch out of the gate and the costs spiral out of control. Obviously, if you are one of those providers that ended up in court over fees or even inadequate or improper processing of ESI, your reputation will be forever spoiled.
There are a lot of certifications a forensic examiner can obtain. What is the value of certification? How should buyers of EDD services evaluate their forensic examiners?
Certifications are a good starting point, although I think they have lost their value over the last several years. Perhaps the tests are getting easier, but I’m seeing folks with forensic certifications that shouldn’t be trusted with a mouse in their hand. Don’t just look to forensic certifications either. Other technology (network, operating system, database, etc.) certifications are also valuable. Check CVs. Do they speak, write and have previous experiences testifying? One of the best methods of evaluation is referrals. Did they do a quality job? Were they on time? Did the costs fall within budget?
You’ve done a lot of work in family law cases. In cases where emotions are running high, how do you counsel clients? Is there a way to talk to people about proportionality when they are angry?
You’ve hit the nail on the head. There is very little logic in family law cases, especially when emotions are running high. I’ve lost count of the number of times we’ve told clients NOT to spend their money on continuing or even starting a forensic analysis. Some listen and some don’t. The exception is where there are issues pertaining to the welfare of any children. We had one case where dad was into BDSM and exhibiting similar behavior towards the children. Mom had no job and was extremely brutalized from the abuse over the years. We completed that case pro bono as it was the right thing to do. Dad lost custody and ordered supervised visitation only.
There has been a lot of hype about EDD services for small firms. In your experience, is this becoming a reality? Can small and solo firms compete with large firms for more EDD cases?
Electronic evidence plays a part in more and more cases. There is a crying need for better tools and methods to review ESI in the smaller cases. Thankfully, some vendors are listening. Products like Digital Warroom and Nextpoint’s products are very affordable for the smaller cases and don’t require a large investment by the solo or small firm attorney. These are hosted solutions, which means you are using the cloud. Large firms are also using hosted solutions, but may use other vendor products depending on the type of data (e.g. foreign language) and/or volume.
You testify in a lot of cases as an expert witness. What are the reasons your services might be needed in this area? What are common reasons that forensic evidence is being challenged, and how can legal teams avoid being challenged?
The good news is that less than 10% of our cases end up going to trial. As we say in the forensic world, “The truth is the truth.” Once we have had a chance to analyze the evidence and report the findings, there are rarely any challenges. That’s what a forensic exam is all about- being repeatable. The opposing party’s examiner better find the same results. The challenge may come from the interpretation of the results. This is where experience and knowledge of the expert comes into play. Many of the forensic examiners today have never used a computer without a graphical interface. Remember the Casey Anthony case? I cringed when I heard the prosecution testimony about the activity surrounding the Internet searches. It failed the smell test in my mind, which ended up being true since the expert later admitted there was a problem with the software that was used.
Would you recommend a similar career path to young technologists? What do you like about being a forensic examiner?
Some universities are now offering degrees in Digital Forensics or some similar name. I’m not sure I would go the route of computer forensics as a baseline. I’m seeing more activity in what I would call digital investigations. This includes network forensics and dealing with cases such as data breaches. We are doing more and more of these types of exams. It’s sort of like following the data trail. Probably the single best thing about being a forensic examiner is getting to the truth. Since we also do criminal defense work, there are many times that we’ve had to call the attorney and tell them that their client needs a new story.
Thanks, John, for participating in the interview!
And to the readers, as always, please share any comments you might have or if you’d like to know more about a particular topic!